- Home » News » World News
80% of critical organisations suffer ransomware attacks

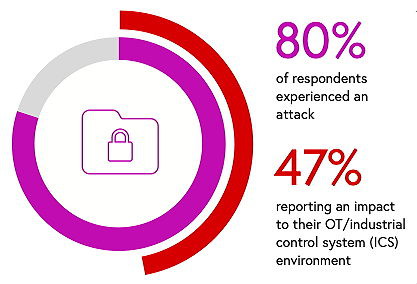
A global survey of 1,100 IT and operational technology (OT) professionals working in critical infrastructure organisations has revealed that 80% experienced a ransomware attack in the past year – almost half of these affecting industrial control systems – and that more than 60% of them paid the ransom, the majority paying at least $500,000 to the cyber-attackers.
According to the survey, conducted for the cyber-security firm Claroty, most of those who paid the ransom estimated their losses in revenue per hour of downtime were at least as big as the payout. And even among those who did pay the ransom, 28% experienced substantial impacts to their operations for more than a week.
Claroty says that the findings suggest that, despite the well-known downsides of paying ransoms, the alternative (revenue losses resulting from prolonged downtime) is too costly for most victim organisations to accept.
The report, The Global State of Industrial Cybersecurity 2021: Resilience Amid Disruption, cites the combination of accelerating digital transformation and the limited availability of skilled cybersecurity workers, as important factors in the attacks on critical infrastructure. In response to the attacks, many executives have become more closely involved in overseeing their organisation’s cybersecurity practices. At least 60% of the organisations quizzed are centralising both their OT and IT governance under a “chief information security officer”, or Ciso.
Nearly 90% of respondents are looking to hire more OT security staff, but 54% report that it is hard finding suitably qualified candidates.
More than 80% of respondents report that they have increased their IT and OT/ICS security budgets since 2020. Implementing new technologies is their top cybersecurity priority, with the oil and gas and IT hardware sectors leading the way. Training is second.
Almost two thirds (62%) support the idea that governments should enforce mandatory reporting of cybersecurity incidents that affect IT and OT/ICS systems. More than 90% of the organisations that suffered cybersecurity incidents say that they reported them to their shareholders and/or authorities.
Although more than 65% of those quizzed rate their organisation’s vulnerability management strategy as being “moderately to highly proactive”, ransomware attacks are still being successful. Claroty suggests that this could be due to the fact that nearly 30% are sharing passwords and only 44% use VPNs – two areas where resilience can be strengthened in OT environments.
“Our research shows that critical infrastructure security is at a pivotal juncture, where threats are proliferating and evolving, but there’s also a growing collective interest and desire in protecting our most essential systems,” says Claroty CEO, Yaniv Vardi. “Security leaders looking to take their programs to the next level must account for all cyber-physical systems in their risk governance practices, segmenting their IT and OT networks and assets, extending their general IT cybersecurity practices to their OT devices, and consistently monitoring for threats across all networks.”
More than half (55%) of the organisations surveyed have revenues of more than $1bn.
Claroty: Twitter LinkedIn Facebook