- Home » News » World News
Rockwell issues updates to plug PLC vulnerabilities

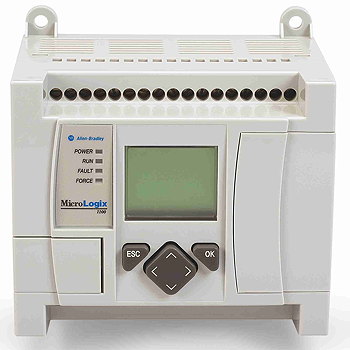
Rockwell Automation has issued firmware updates for some of its Allen-Bradley MicroLogic 1100 and 1400 PLCs to tackle security vulnerabilities that, if left unpatched, could allow remote cyber-attackers to interfere with the PLCs’ operation.
Cyber-security analysts have identified a series of vulnerabilities, one of which – called FrostyURL – could be exploited using a single malicious Web address (URL) which could appear to be an internal link in an email. “It blew our minds how simple it is,” says Nir Giller, chief technology officer at the cyber-security specialist, CyberX, which identified the flaw.
Other vulnerabilities in the PLCs were identified by cyber-analysts at Positive Technologies and Elastica. They include:
• a stack-based buffer overflow vulnerability that may crash the PLC or allow arbitrary code to be executed;
• a memory buffer problem that could allow a Web request from a remote attacker to crash the PLC;
• the ability to upload dangerous files that remote attackers could use to direct external Web content, including remote files, into the PLC’s Web page frame;
• a cross-site scripting vulnerability that could allow attackers to inject and store Javascript in the PLC’s built-in Web server, which would be executed on the user’s Web browser when accessing the server; and
• a SQL injection weakness that may allow an attacker to create new users, delete users, or escalate privileges by getting an administrator to execute a specially-crafted link.
Although there is no evidence that these vulnerabilities have been exploited to date, the US Government’s Industrial Control Systems Cyber-Emergency Response Team (ICS-Cert) is warning that an attacker with low skills could exploit them.
The new firmware versions issued by Rockwell are designed to mitigate all of the reported vulnerabilities in the affected PLCs, except for the buffer overflow in affected MicroLogix 1400 PLCs. The company is working a new firmware version to fix this, which is due to be released soon.
Rockwell has issued a security notification which can be accessed from its Web site by users with a valid account.
The company recommends that users of the affected PLCs evaluate the impact of each vulnerability within their own environment, and apply the following mitigations:
• update the affected PLCs with the appropriate firmware update;
• disable the PLCs’ Web servers, which are enabled by default;
• set the keyswitch to Hard Run to prohibit re-enabling of the Web server via RSLogix 500 software;
• use trusted software, software patches, anti-virus/anti-malware programs, and interact only with trusted Web sites and attachments; and
• implement training and awareness programmes to educate their staff on warning signs of phishing or social engineering attacks.
Rockwell also recommends subscribing to its Security Advisory Index, which contains the Knowledgebase article KB: 54102 and provides up-to-date information on security matters affecting its products.
In an advisory notice on the PLC vulnerabilities, ICS-Cert recommends that users take defensive measures to minimise the risk of exploitation. In particular, users should:
• minimise network exposure for all control system devices and/or systems, and ensure that they are not accessible from the Internet;
• locate control system networks and remote devices behind firewalls, and isolate them from business networks; and
• when remote access is required, use secure methods such as VPNs (virtual private networks), but be aware that VPNs may have vulnerabilities and should be updated to the latest version. VPNs, it points out, are only as secure as the connected devices.