- Home » News » World News
Malware targets industrial controls and OPC servers

Cyber-security organisations have issued warnings about a malware campaign that has targeted industrial control systems (ICS) from at least three suppliers, including systems running OPC servers.
The campaign, known as Dragonfly or Energetic Bear, is thought to originate in Eastern Europe – probably Russia – and uses various techniques to infect control systems. Its origins have been traced back to 2011 or before, and the group behind it could have hacked systems at more than 1,000 organisations in more than 80 countries over the past 18 months.
Originally the group targeted defence and aerospace organisations in the US and Canada before moving on to American and European energy firms in 2013. The main purpose of the cyber-attacks appears to be industrial espionage, but the cyber-security specialist Symantec points out that if the group exploited the sabotage capabilities open to them, they could damage or disrupt control systems and energy supplies in the affected countries.
According to Symantec, Dragonfly’s most ambitious attack strategy has been to infect software from ICS equipment suppliers with a RAT (remote access type) Trojan so that when end-users download software updates from their suppliers, they unwittingly install the malware on their systems. The malware, known as Havex or Oldrea, was first found in a product used to provide VPN (virtual private network) access to PLCs. By the time the vendor discovered the attack, there had been 250 downloads of the compromised software.
Another supplier that was attacked was a European manufacturer of specialist PLCs. In this case, a software package containing a device driver was compromised and was available for download for at least six weeks in June and July 2013.
A third firm to be attacked was a European business that develops systems to manage wind turbines, biogas plants and other energy equipment. Symantec believes that the compromised software was available for download for around ten days in April 2014.
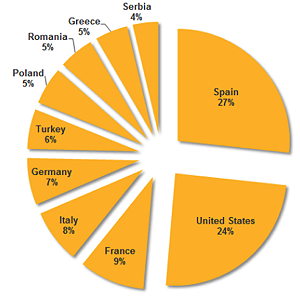
Another cyber-security specialist F-Secure says it has found and analysed 88 variants of the Havex RAT used to gain access to, and harvest data from, industrial networks and machines. It traced around 1,500 IP addresses to identify potential victims and found that the malware had contacted 146 command and control (C&C) servers. The attackers used compromised Web sites – mainly blogs – as C&C servers.
According to F-Secure, the attackers are interested not only in compromising the networks of targeted organisations, but are also motivated to control their ICS and SCADA systems. “The source of this motivation is unclear to us,” F-secure says.
F-Secure has identified three industrial control software vendors whose Web sites were broken into and legitimate software installers were trojanised to incorporate the Havex RAT. “We suspect that more similar cases exist, but have not been identified yet,” it adds.